I’ve always been fascinated by how attackers find vulnerabilities and target products or target companies with certain products. Having been part of the cybersecurity ecosystem, learning about concepts and keeping up with the news, has always been a challenge for me. With the success of Nginx Proxy Manager app, I figured I could use AI to help me build an app for this, this is the story of CyberPrism App.
Fundamentally, I despised that a lot of cybersecurity actionable intelligence was hidden behind expensive tools.
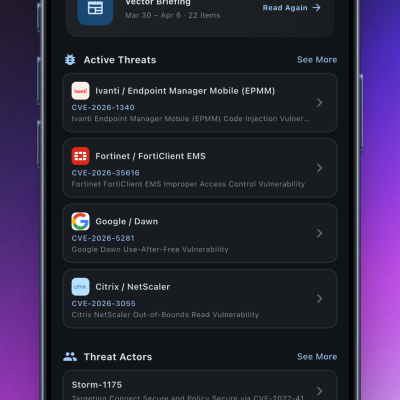
I wanted to know, I just wanted to know what is happening — map vulnerabilities to products to threat actors. I needed something that worked on my phone, between meetings, in five minutes. I wanted to be aware and knowledgeable about these things. I looked around and it didn’t exist; so, I built it — that’s CyberPrism App. And the ideas started to evolve.
How it started: Exploited Vulnerabilities and AI from day one
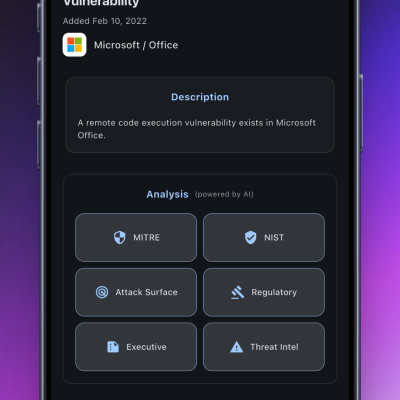
I built it with AI – Cursor, the first version was an automated catalog of Known Exploited Vulnerabilities that showed the product, the company, and contextualized the vulnerability across NIST, MITRE, Regulatory risks, Attack Surface vectors. I wanted to turn this into one of the most ambitious projects for me:
- I wanted Android and iOS apps (cyber folks love Android for some reason)
- I wanted to have the data
- I wanted it to be modular so I can add more and keep building into it as a platform
- I wanted to build for scale, I estimated at least 10k+ users in 6 months; this meant:
- it needed a reliable and scalable infrastructure – webserver, app server, database, cache, etc.
- save on hosting costs and lag so figured I could host the entire thing in my homelab
- This had to be fully automated with no intervention for me unless something broke
With those product principles in mind, this was the first pipeline I built ground up:
Get the feed -> store in my database -> send stuff to an AI -> get responses -> store in the database -> setup APIs -> show information in the app
Once it started working, it helped me get better about separating noise and signal. And then I decided to tackle another thing that always made me feel dumb and clueless — the damn threat intel articles. Oh god, these are so dense and, in my view, great candidates for AI to simplify.
How it evolved: AI everywhere
Now that I had:
- CISA’s KEVs coming in
- Threat intel articles coming in identifying threat actors and CVEs
- My system mapping those CVEs against the KEV database
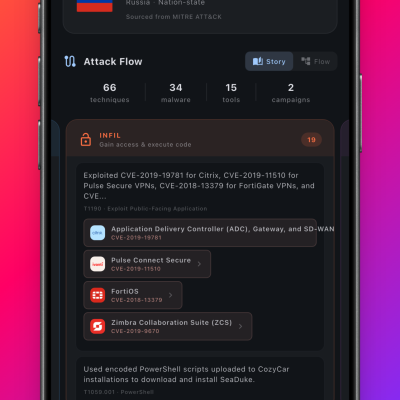
I was able to create threat actor cards enriched with publicly available information. My goal of Threat Actor -> CVE -> Products, was accomplished. I wasn’t done, though. The more I used the app, even this started becoming noise because I couldn’t filter to products or vendors I cared about.
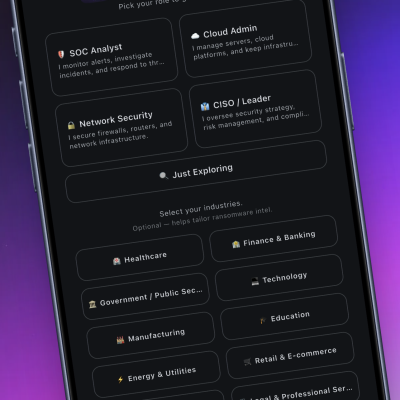
And thus began the new refactor, it also coincided with the release of Opus 4.6. This was the most fun I was having with vibecoding. It was truly idea to prototype within hours. I also learned about mobile apps needing onboarding. So, the result was:
Pick a persona (e.g., CISO) -> pick your industry -> pick your products -> a customized feed for you
- You’re a CISO and want to know if there are CVEs in your tech stack? Send them to your Attack Surface or patching teams? There’s an app for that – CyberPrism App
- You’re a CISO and want to see which companies in your industry are being breached? There’s an app for that – CyberPrism App
- You’re a SOC analyst and want to read up on the risk impact of a CVE or have a PDF that shares the details about a CVE with your cyber risk team? There’s an app for that – CyberPrism App
- You’re a cyber consultant and want to satiate your curiosity about cybersecurity? There’s an app for that – CyberPrism App
- You’re a cloud engineer and want to be sometimes ahead of your cyber team members? There’s an app for that…
With all this being in the app and per user, I made the feature I’m most proud of – Weekly AI-generated threat intel briefs. Again, fully automated. Here’s a sample:
How I actually use it
When a KEV drops, my phone buzzes. I tap it, I’m looking at the full AI analysis before my team has had a chance to brief me on it. When my threat intel team brings a threat actor to my attention, I have an idea about the actor’s profile, which CVEs they’re using, and which of our vendors are exposed. When my attack surface team is tracking a breach, I’ve already seen it in CyberPrism App — I can ask sharper questions.
Sometimes I’m the one sending things to my teams — a breach in our sector I spotted in the app, a KEV that dropped overnight, a ransomware group that’s been active in healthcare this week.
Another personal validation was when I created CyberPrism’s 2025 recap, the data said manufacturing was ransomware’s biggest target; FBI’s 2025 recap said the same.
Building it mobile-first — actually mobile-first
I’ve written about my app stack before — Cursor, Flutter, Github, CodeMagic. Flutter gave me Android and iOS from a single codebase, which matters when you’re one person building this in your spare time. CodeMagic handles the App Store build pipeline without me needing a Mac. Cursor writes the code. I describe what I need, I have 15 years of domain expertise in why it matters, and AI handles the implementation.
I was pulling Known Exploited vulnerabilities, I was pulling technical threat intel, I was pulling breached companies and near-real-time alerts about ransomware breaches, I had all of this customized to industry and products. I threw news articles into my AI pipeline to pull latest breaches. I had a cyber platform in a mobile app running on its own, using AI through every step.
There are several mobile-first features:
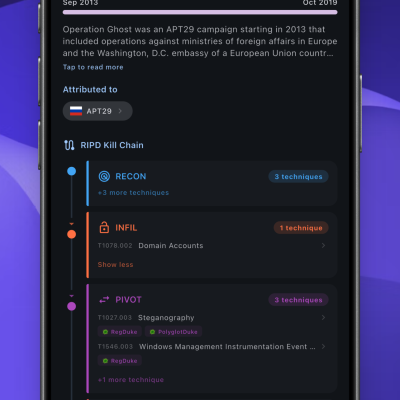
- The UI is modern-phones friendly, including a custom adaption of the MITRE framework to track how threat actors attack
- Push notifications are deeplinked and robust
- Search, cloud sync, bookmarks, offline reading
Screenshots:
This is where I’m hosting it:

Who else it’s for
I built this for anyone in an organization who touches security decisions — cloud engineers, GRC analysts, IT ops, enterprise risk consultants. People who need this context to do their jobs well but don’t have a SOC feeding them threat intelligence every day.
Core features are free. Pro is $39.99/year. Expense it. There’s no procurement process in the world that should stand between someone doing a security job and knowing what’s happening in the threat landscape that affects them.
I built this hoping to get easily 10k+ users in the first 6 months and scale from there. I have about 600 users across iOS and Android.